Is SumatraPDF affected by the new ‘Shadow Attack’ that can replace content in digitally signed PDF files?
Home / Is Sumatra vulnerable to the new ‘Shadow Attack’?


Generally no, it’s most likely not listed because it does not support many such exploitable features.
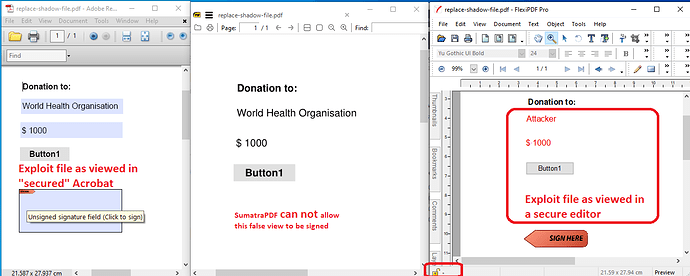
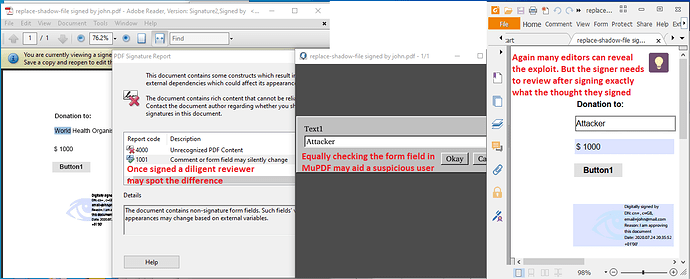
In many respects this is a variation on earlier and future exploits, PDF’s can carry many payloads, but only one needs to be shown to fool an observer.
EVERY PDF VIEWER (including those “unaffected”) should show the false information otherwise it would not be a valid PDF viewer ! SumatraPDF currently does not allow the victim to sign, thus the exploit cannot proceed.
and unlike those “affected” SumatraPDF has no signature verification to show that it is to be trusted.
Personally having used Acrobat automated tasks to send back users data, I am against SumatraPDF allowing for handling Personal XFA data or False Signatures, but that’s just me as a Luddite individual. Most users request such insecurities to match what adobe does. IMHO digital signatures just like “wet” signatures will never be 100% unforgeable, so why bother telling people to trust them as genuine. It’s revenue for the app sellers, the hackers, the finger waggers, save a fortune and dont trust any of them. / end rant.
A PDF can contain actions that alter the interface, goto a set page, carry out scripted actions and even just simply report which IP address opened which text or images. SumatraPDF currently does not support many* such actions, but that does not stop users requesting them !
- Since PS files’s (which PDFs are based on) can contain self adjusting code it is possible to observe Post Script pages as run through GhostScript changing appearance on each refresh within SumatraPDF. But as a variable printer format I strongly feel PS files should not be used to imply any authority. If you have Ghostscript installed then trust me and open this file press R to see the page change.
CHM files are also dynamic thus can change themselves just like cartoons so those also should never be given credence as “safe” click here to download an anim images only chm (unzip to view contents).